I know nothing about what Apple is going to announce at an iPhone event expected on Sept. 10. But I do know about one feature the is a strong candidate and definitely should be included in the next generation of iPhones and iPads: a fingerprint reader.
There are two basic reasons why Apple should–and, I believe, likely will–do this. First, as a result of its 2012 purchase of AuthenTec, Apple owns advanced fingerprint sensor technology that gives it a real competitive advantage. Second, incorporating the technology, with the sort of software support that Apple customarily delivers, will bring real benefits to customers and help strengthen the iOS ecosystem.
Biometric reliability. Fingerprint technology has been around for a very long time, but only recently has it gotten reliable enough to be truly useful. They would reject your finger if your skin was too moist or too dry, or if you swiped too fast or too slow or at an angle. Recent sensor-equipped laptops that I have used read my fingerprint quickly and accurately nearly every time.
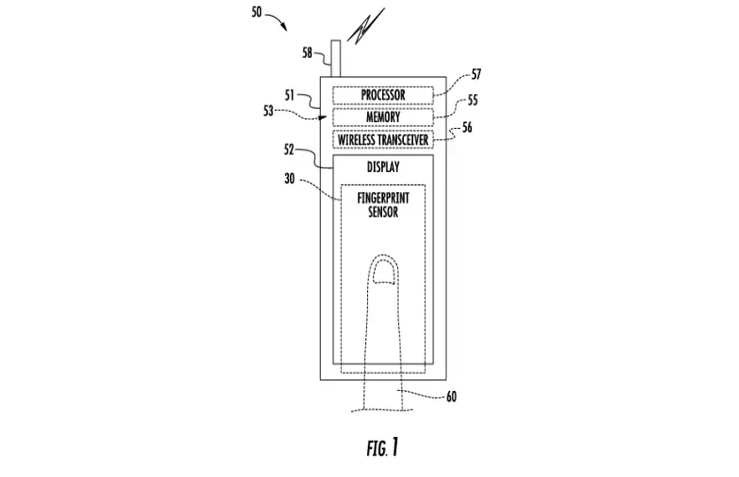
Rumor has it that Apple will build a sensor into the home button, a move that seems both likely and practical, since tapping the home button is a common way to wake a sleeping iPhone or iPad. Apple has a patent pending for technology that would embed the sensor in the display itself (illustration above), but it seems unlikely that it would be ready for use any time soon.
The consumer benefit of fingerprint technology is clear. I suspect most iPhone owners have not activated even Apple’s PIN code login protection, which is not a great idea, although having to enter the code every time you want to use the iPhone is a nuisance. The real issue comes with the greater use of handsets as payment devices. For this to work well, you need something stronger than simply possession of the device to authenticate purchases unless you want anyone who happens to get hold of your phone to be able to buy stuff with it. Better authentication is a key to making both buyers and sellers more confident about using phone-based payment systems.[pullquote]Better authentication is a key to making both buyers and sellers more confident about using phone-based payment systems.[/pullquote]
A big improvement. Two-factor authentication is a big improvement, with the rule of them being you need two of three of something you have, something you are, and something you know. The phone is something you have and a biometric–your fingerprint–is something you are. The advantage of a fingerprint is that it’s easy and natural to collect, giving the user the benefits of stronger authentication with little or no effort.
But with authentication, as with all security-related matters, the devil is in the implementation. Biometrics pose a special challenge. If your password is compromised, you get a new password. If your fingerprint is compromised, you cannot grow a new finger. For this reason, your fingerprint should never be stored, not in a database (which is why the stories about Apple acquiring a lucrative fingerprint database and the privacy fears related to it are nonsense) not even on the device itself.
Keeping it secure. The “fingerprint” collected by a sensor actually consists of a map of “minutiae,” specific features of a print, that can be converted into a numerical code. This code is then hashed, run through a one-way mathematical function that will always supply the same output from a given input, but which makes it impossible to compute the input from the output. All the authentication system, whether on the device or on a server, ever sees is the hash. If it matches, you’re good to go; otherwise, your login is rejected. (Password systems should word the same way, unfortunately, many don’t.) The trick is picking a function that makes it very, very rare for two inputs to produce the same output and especially, all but impossible to force such a “collision” to occur. The way to do this is to use a standard, well-tested cryptographic hash algorithm, such as the National Institutes of Standards & Technology’s SHA-2 family.
Apple certainly has the software chops to implement biometrics in a way that is both secure and very user-friendly. If it pulls it off, the $356 million it paid for AuthenTec could prove to be money very well spent.
Uh oh. I just jumped to Android and ChromeOS after decades of Apple loyalty. This might be a real game-changing feature. I have long disparaged using handsets as payment devices. Fishing one out, swiping it open, finding and launching the relevant app, and telling it to make the payment seems to be to be less, not more convenient than simply using a credit card. But if all you have to do is fish and swipe your fingerprint, then that’s different…
I like this site. But could you run things through a spell-checker before posting, please?
I do not see Apple ever collecting such personal information it could be forced to surrender. Steve, you explained incredibly well the process which Apple might use to avoid getting into such a predicament.
I can’t remember Mark Twain’s quip on spelling and its lack of imagination but here is a little site on his opinions on spelling that may help temper such concern.
http://www.twainquotes.com/Spelling.html
Some really excellent info, Sword lily I detected this.